A forward-confirmed reverse DNS check (https://en.wikipedia.org/wiki/Forward-confirmed_reverse_DNS) is an increasingly common anti-spam measure on mailservers, which checks the sending IP of an email to see if the hostname returned has a DNS record matching that same IP address.
For example, if an email reaching a mailserver were to have a sending IP of 127.0.0.1, the server will perform a host lookup on that IP. If the hostname returned is 'server.example.com' the mailserver will then check the DNS record for 'server.example.com'.
Now, say the DNS record for 'server.example.com' does not exist or returns a different IP of 127.2.2.2. If this is the case, since the message claims to be from 'server.example.com' but 'server.example.com' does not resolve to that sending IP address of 127.0.0.1, there is a possibility that the message may be forging the sending host, and the mailserver will reject that message. If, however, the 'server.example.com' record points back to that 127.0.0.1 address that it was sent from, the FCrDNS check passes, and the message will move on to the next checks, and/or complete delivery.
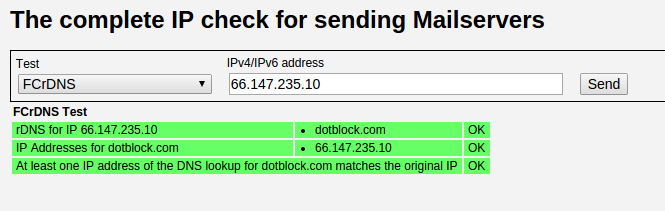
Here's an example of that check in action:
The purpose of a FCrDNS check is to cut down on the amount of incoming spam that is processed by the mailserver. Since this check typically happens as soon as a connection is made, before any other header information is sent, a server can reject suspicious messages more efficiently, since it would not be wasting resources processing that header information from suspect senders. Because spammers often forge information in headers to make it seem like they're coming from other hosts, or perhaps send messages via malicious scripts injected into unrelated websites, the messages will often fail the FCrDNS check. Legitimate senders, however, should typically have these records setup correctly, and may likely never notice that the check is occuring.
You can check to see if your sending IP passes a FCrDNS check here:
http://multirbl.valli.org/fcrdns-test/
Please contact support if you have any questions!